Navigating the future of higher education: A digital-first approach to the student journey
Insights from the UCISA Leadership Conference, Edinburgh.
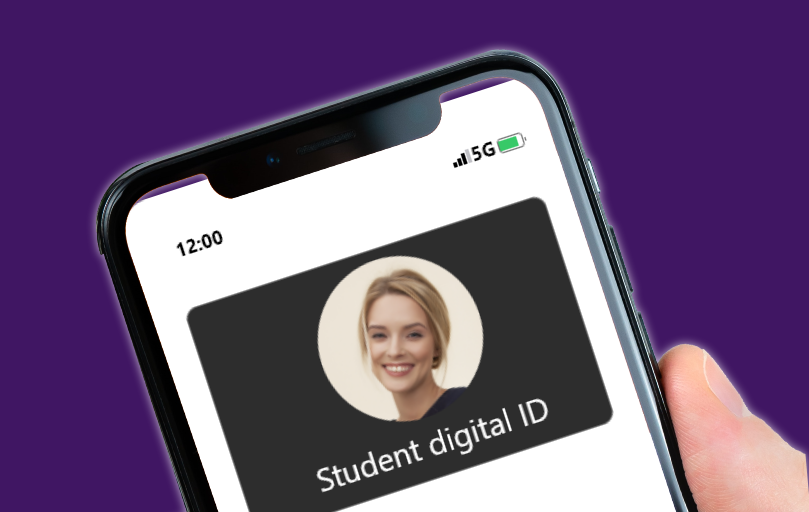
The move to a passwordless society
Many of us are familiar with FaceID, two-factor authentication and banking apps that need another level of verification, so could dynamic authorisations, zero-trust and identity-first authentication take centre stage and see passwords off for good?
Be the first to hear about news, product updates, and innovation from proofid